The Marriott data breach is one of the biggest we’ve seen, certainly the biggest in travel. There are hundreds of millions of records, and even millions of compromised passports. There’s probably even proprietary data that’s been compiled on you which has been taken that they haven’t even disclosed.

There are several things you can do to protect yourself from hacks but most of our identifying data has already been taken in various data breaches. Companies have to do better.
Hackers even pay out points to get people to help them, so loyalty programs can learn a thing or too. United has a bug bounty program paying out up to a million miles for identifying vulnerabilities.
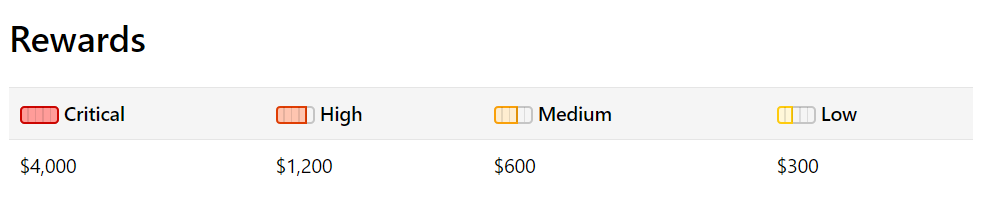
Now Hyatt has a bug bounty program, too. (HT: Traveling for Miles) They’ll pay out up to $4000 per vulnerability:
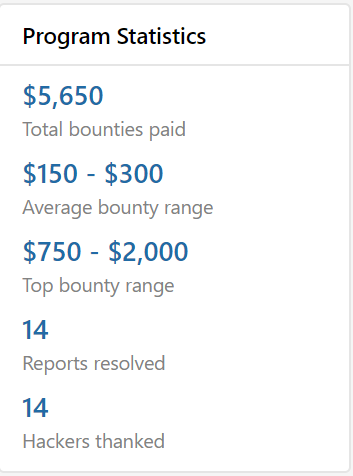
It’s a new program, they’ve already had submissions and payouts, though most have been small:
I’ve never thought much of Hyatt’s IT, but whether or not it’s functional isn’t the issue here. How easy is it to infiltrate or bring down?
Bear in mind that if your strategy for identifying eligible issues involves code injection on live systems, DDOS attacks, or physical intrusions, you could go away for a very long time. But if you can hack World of Hyatt and roll everything back to Gold Passport? Totally worth it.


I don’t know any coders in the US who would waste their time for this type of payout. This program must be outsourced to foreigners.
BUILD THE FIREWALL!!